Intelligence is Your First Defense
Paragon Graphite Spyware Exposed: LinkedIn Blunder Reveals Zero-Click Surveillance Tools
In early February 2026, Paragon Solutions' chief compliance officer accidentally exposed their Graphite spyware dashboard in a LinkedIn event photo. The leaked UI revealed active surveillance of target "Valentina" (Czech number), showing zero-click intercepts of WhatsApp, Signal, Telegram & more. This stunning OPSEC blunder reignited global debate on spyware ethics, privacy threats, and the shadowy world of commercial surveillance tools.
CYBERSECURITYEVOLVING TECH CYBER WARFARE
Phillemon Neluvhalani
2/22/20264 min read


Paragon Solutions, founded in 2019 by former Israeli intelligence officials including ex-Prime Minister Ehud Barak,
positions itself as a provider of "ethical" surveillance tools

However, We can clearly see that tools like Graphite are frequently abused to target journalists, activists, human rights defenders, and political opponents.
The company has faced scrutiny before, with reports linking its spyware to attacks in Europe, the United States, and beyond.
Details of the Incident: What Was Exposed?...
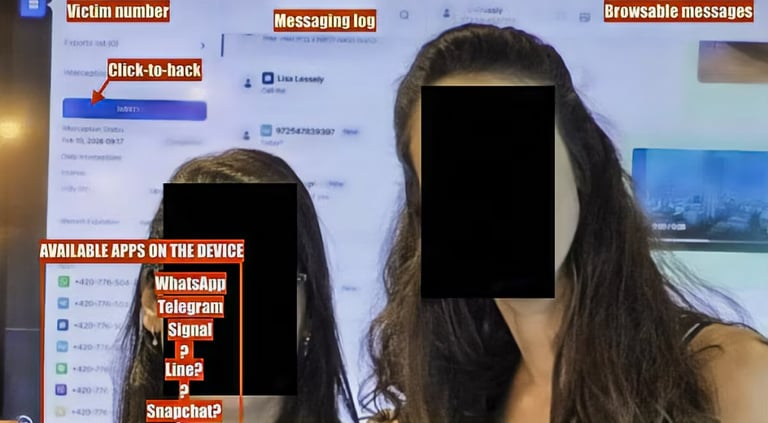
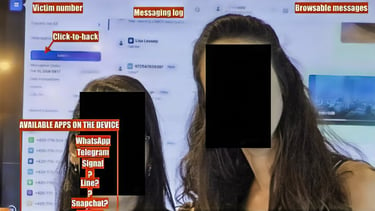
The leaked screenshot, by Paragon's general counsel and chief compliance officer, Reut Yamen, depicted a live operational dashboard. It showed real-time interception logs marked as "completed," along with interfaces for extracting data from encrypted messaging apps such as WhatsApp, Signal, Telegram, Line, Snapchat, and TikTok.
The target "Valentina" was highlighted with a Czech phone number, suggesting an ongoing or recent surveillance operation. Annotations from cybersecurity researchers on social media identified toggles for remote device access, microphone and camera activation, and full data exfiltration capabilities.
This exposure was described as a "major OPSEC fail" by experts, highlighting the irony of a surveillance company failing to secure its own internal visuals.While some speculated the leak might have been intentional, perhaps for marketing or deterrence purposes, most analyses point to it being a genuine accident.
Is This an Isolated Incident?
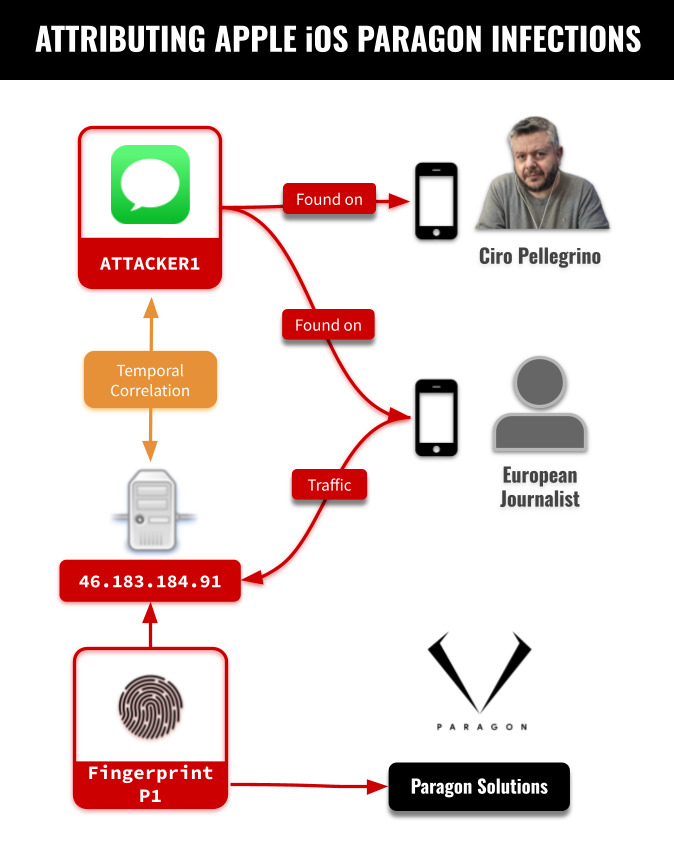
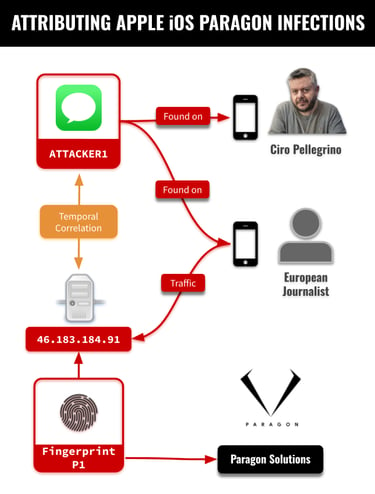
Far from being a one-off mishap, the LinkedIn leak underscores a pattern of vulnerabilities and abuses in the commercial spyware sector. Paragon's Graphite has been implicated in multiple high-profile cases prior to this event. In June 2025, a FreeType zero-day vulnerability (CVE-2025-27363) was exploited in attacks linked to Paragon, allowing remote code execution on devices via malicious PDFs in WhatsApp groups.
This exploit was part of a broader campaign targeting journalists and activists.
Moreover, Paragon has contracts with entities like U.S. Immigration and Customs Enforcement (ICE), which reportedly used Graphite in a $2 million deal to monitor anti-ICE protests.
Reports indicate Graphite deployments in countries including Australia, Canada, Europe, Israel, Singapore, and the U.S., often against civil society figures.
Around Early February 2025, Paragon is said to have terminated a contract with Italy following allegations that its spyware targeted an investigative journalist and activists critical of the government.


These incidents suggest that while the LinkedIn leak is isolated in its method of exposure, the underlying surveillance operations are systemic and widespread.
The spyware industry as a whole is rife with similar scandals. Competitors like NSO Group's Pegasus have been blacklisted by the U.S (so they claim). for similar abuses, yet companies like Paragon continue to operate, often rebranding or relocating to evade regulations.
This leak is just the latest in a series of revelations that highlight the industry's opacity and the challenges in holding it accountable.
Who Is Compromised: Just "Valentina" or a Broader Threat?
The exposed dashboard specifically referenced "Valentina" and her Czech phone number, indicating a targeted operation against an individual.
However, this does not imply that only she was affected. Graphite is designed for mass surveillance capabilities, sold to governments that can deploy it against multiple targets simultaneously.
The interface shown suggests a system capable of handling numerous intercepts, with logs for completed operations implying ongoing activities.Not all users of apps like WhatsApp or Signal are compromised; Graphite employs targeted attacks rather than blanket surveillance.
That said, the tool's proliferation means thousands could be at risk globally. WhatsApp has reported Graphite being used to target at least 90 individuals across two dozen countries, including journalists and civil society members.
The leak raises questions about how many undisclosed victims exist, as Paragon's clients include authoritarian regimes and democratic governments alike.
Methodology of Access: How Does Graphite Compromise Devices?
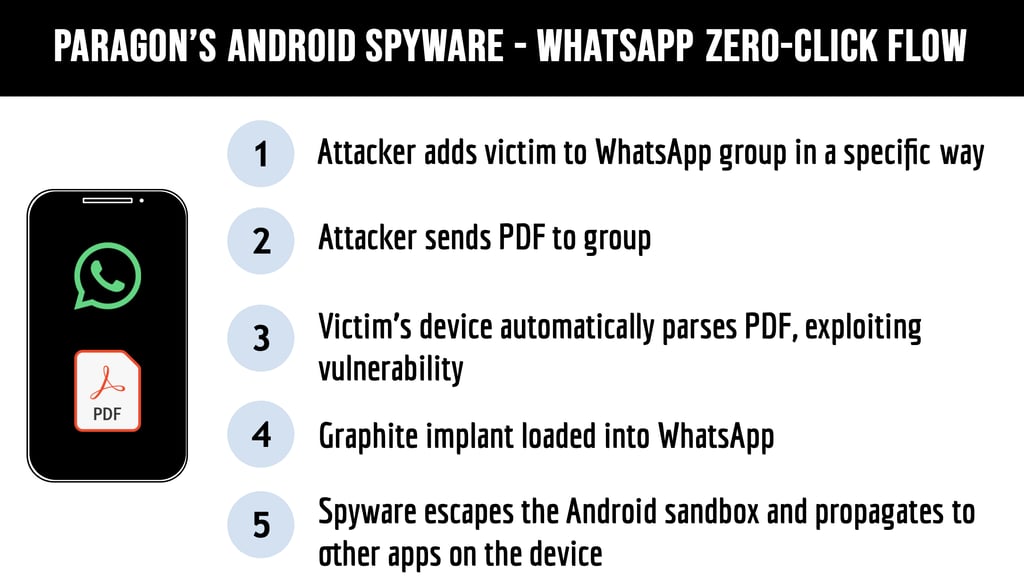
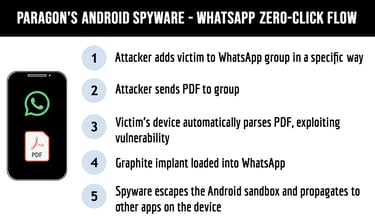
Graphite's power lies in its use of sophisticated zero-click exploits, which infect devices without requiring any user interaction.
Common vectors include vulnerabilities in messaging apps like iMessage or WhatsApp. For example, attackers might add a victim to a specific WhatsApp group and send a malicious PDF that exploits parsing flaws, such as the aforementioned FreeType vulnerability.
Once infected, the spyware escapes app sandboxes, propagates to other applications, and grants full remote access.Access is primarily through the phone or device itself, not directly via user accounts.
By compromising the operating system (iOS or Android), Graphite can intercept encrypted communications in real-time, even from end-to-end encrypted apps.
This includes reading messages, accessing files, tracking locations, and activating hardware like cameras and microphones.
The methodology relies on chaining zero-day vulnerabilities undisclosed flaws in software that are patched only after being exposed, deliberately leaving a window for exploitation. In the case of "Valentina," the dashboard indicated app-level data extraction, likely achieved post-infection via a phone-based implant.
While account credentials might be harvested secondarily, the initial breach is device-centric, making it insidious and hard to detect.Broader Implications and the Road Ahead, This incident reignites calls for stricter regulations on the spyware industry. The U.S. has already imposed export controls on similar tools, but enforcement remains uneven.
Let's be realistic "ethical" spyware is a myth, as these tools inevitably enable human rights abuses.
For individuals, the leak serves as a reminder to use security best practices: keep devices updated, avoid suspicious links, and employ antivirus software capable of detecting advanced threats. As we continue, analyzing the leak for more insights, the Paragon incident exposes the fragile line between security and surveillance.
What started as a LinkedIn faux pas may catalyze real change, or it could be just another footnote in the ongoing battle for digital privacy.